-
Business Consulting
Our business consulting specialists offer a comprehensive blend of strategic advisory services. We assess the business, industry, operating model, synergy, skill sets and vision of the organisation and recommend the way forward
-
Digital Transformation Services
Grant Thornton’s digital transformation services help traditional businesses digitalise their business models with cloud technology, IoT consulting, app development and more DigiTech solutions.
-
Human Capital Consulting
Our Human Capital Consulting team harnesses technology and industry expertise to assist in constructing adaptable organisations with transparency, fostering productive and value-driven workforces, and inspiring employees to engage meaningfully in their tasks.
-
Production Linked Incentive Scheme
Production-linked Incentive Scheme by the Indian government is aimed at boosting manufacturing. Grant Thornton Bharat offers varied services across sectors to help businesses avail of this scheme.
-
Public Sector Advisory
Our Public Sector Advisory team has focused streams, aligned with the core priorities of the Government of India. We are responsible for providing innovative and customized technical and managerial solutions.
-
Tech Advisory
We have amalgamated Digital Transformation, IT Advisory & Information Management and Analytics into a new offering, DigiTech.
-
Direct Tax services
Our tax specialists offer a comprehensive blend of tax advisory, tax litigation, regulatory and compliance services, helping you navigate through complex business matters.
-
Indirect Tax Services
Get tax advisory service by leading tax firm Grant Thornton India. Our indirect tax services include advisory, compliance and litigation services for corporate, international and transaction tax
-
Transfer pricing services
Our transfer pricing services experts provide a range of services from provision of APA services to handling large global assignments including Country by Country reporting.
-
US Tax
At Grant Thornton, we help individuals and dynamic companies deal with US tax laws, which are one of the most complicated tax legislations across the world.
-
Financial Services - Tax
Best financial advisory services, tailored for small and large businesses by the experts having comprehensive knowledge of domestic laws and access to multifaceted tools to provide a valuable results.
-
Financial Reporting consulting services
Our experts have significant hands-on experience in providing IFRS/US GAAP services, end-to-end solutions and support services to fulfil financial reporting requirements.
-
Fund accounting and financial reporting
International operations often lack standardisation and have varied local reporting formats and requirements. Our experts can offer proactive insights, practical guidance, and positive progress and help meet regulatory timeframes.
-
Compliance and Secretarial Services
Our experts can assist in overhauling the entire compliance machinery of the organisation through evaluation of the applicable statutory obligations, monitoring of adequate governance controls, reporting and providing ongoing support.
-
Global People Solutions
As businesses transcend borders, both domestic and global considerations need equal attention. Our interim CFO and financial controller support services help organisations meet the business vision.
-
Finance and accounting outsourcing
Our accounting experts assist organisations in managing their accounting and reporting. Our dedicated Integrated Knowledge and Capability Centre (IKCC), allows us to service both the domestic and global markets efficiently and cost-effectively
-
Compliance Management System
We have automation solutions for you that will allow meeting government requirements and remain diligent, which when failed, can lead to penalties and loss in revenue.
-
IKCC: Grant Thornton's Shared Service Centre
The India Knowledge and Capability Centre (IKCC), aimed at delivering solutions by developing capabilities, has completed four years of its journey.
-
Global compliance and reporting solutions
At Grant Thornton Bharat, we meet the challenges of our clients and help them unlock their potential for growth. Our professionals offer solutions tailored to meet our clients’ global accounting and statutory reporting requirements. With first-hand experience of local reporting requirements in more than 145+ locations worldwide, we provide seamless and consistent international service delivery through a single point of contact.
-
Related Party Transactions Governance
Related Party Transactions Governance
-
Private Client Services
Private Client Services
-
Labour codes
Labour codes solutions help you transition through the new legislation. At Grant Thornton, we help businesses divide their approach to make sure a smooth transition.
-
Alerts
At Grant Thornton India, with the help of our tax alerts, we help to provide updates on how to minimise your tax exposure and risks.
-
Cyber
In today’s time, businesses have gone through large transformation initiatives such as adoption of digital technologies, transition to cloud, use of advanced technologies et al.
-
Governance, Risk & Operations
Our Governance, Risk and Operations (GRO) services encompass Internal Audit, Enterprise Risk Management, Internal Financial Controls, IT advisory, Standard Operating Procedures and other services.
-
Risk analytics
Grant Thornton Bharat’s CLEARR Insights is a state-of-the art data analytics platform that will help you in seamless data analysis and efficient decision-making.
-
Forensic & Investigation Services
The team of forensic advisory services experts consists of the best intelligence corporate experts, and fraud risk, computer forensic experts to deliver most effective solutions to dynamic Indian businesses.
-
ESG consulting
Grant Thornton Bharat offers holistic ESG consulting solutions for sustainable business outcomes. With industry expertise and AI technology, we drive long-term value.

-
Transaction Tax Services
Our transaction tax experts understand your business, anticipate your needs and come up with robust tax solutions that help you achieve business objectives ensuring compliance and efficiency
-
Deal Advisory
Unlike other M&A advisory firm in India, we offer deal advisory services and work exclusively with controlled and well-designed strategies to help businesses grow, expand and create value.
-
Due Diligence
Grant Thornton’s financial due diligence services are aimed at corporate looking for mergers and acquisitions, private equity firms evaluating investments and businesses/promoters considering sale/divestment.
-
Valuations
As one of the leading valuation consultants in India, Grant Thornton specializes in all the aspects of the process like business valuation services, financial reporting, tax issues, etc.
-
Overseas Listing
Overseas listing presents a perfect platform for mid-sized Indian companies with global ambitions. Grant Thornton’s team of experts in listings, work closely with clients during all stages.
-
Debt & Special Situations Solutions
Grant Thornton Bharat offers specialist debt and special situations consulting services, including restructuring, insolvency, and asset tracing solutions.
-
Financial Reporting Advisory Services
Financial Reporting Advisory Services
-
Financial Statement Audit and Attestation Services
Financial Statement Audit and Attestation Services

- Agriculture
- Asset management
- Automotive and EV
- Aviation
- Banking
- Education and ed-tech
- Energy & Renewables
- Engineering & industrial products
- FinTech
- FMCG & consumer goods
- Food processing
- Gaming
- Healthcare
- Urban infrastructure
- Insurance
- Media
- Medical devices
- Metals & Mining
- NBFC
- Pharma, bio tech & life sciences
- Real estate and REITs
- Retail & E-commerce
- Specialty chemicals
- Sports
- Technology
- Telecom
- Transportation & logistics
- Tourism & hospitality
-
India-UK
India-UK
Author: Samir Paranjpe
The history of fraud dates back to 300 B.C.1, and since then frauds have increased significantly in volume and complexity over the years. Frauds in today’s digital world are highly complex, and vulnerabilities in anti-fraud controls continue to be exploited by fraudsters. The role of a forensic investigator with deep subject matter knowledge and investigation experience has only gained prominence in detecting, investigating and mitigating fraud.
A forensic investigator may appear to many as a prototype of the famous fictional detective Sherlock Holmes. While there may be similarities, the role of a modern forensic investigator, with the ever-expanding fraud vector, is much more multifaceted. It involves unearthing fraudulent activities such as siphoning or embezzlement of funds, financial irregularity, misappropriation of assets or unethical conduct, as well as application of accounting knowledge, analysis of forensic data and interview assessment to name a few.
Broadly speaking, the multidisciplinary field of forensics is a combination of accounting, audit and investigation. The role, understandably, demands a specialised skillset – attention to detail, ability to draw meaningful insights from volumes of data, intuitive mindset and strong communication skills to clearly articulate the facts and findings of any investigation. Thesaurus traces the origin of the word ‘forensics’ to the Latin word forensis, which meant ‘relating to courts of law’. The evidence collected during an investigation must be suitable to produce in a court of law, if required.
Use of the word ‘forensic’ over time
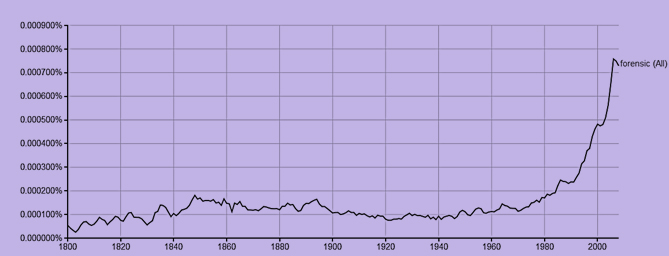
Source: Google Ngram viewer
A dynamic fraud theatre, the challenge of handling tight deadlines and sensitivity of situations make a forensic investigator’s typical day hard to define. More often than not, it is a race against time because the sooner the modus operandi and evidence are discovered, the lesser is the subsequent damage.
The day may begin with analysis of digital evidence and forensic imaging to track a payment fraud. This would follow review of documentation to identify a false third-party transaction. While reviewing these datasets to detect anomalies, there could be an ethical lapse reported elsewhere and a subsequent visit to understand the concern would follow. Next in the list would be prepping for a suspect interview in the next few hours, followed by a site visit to validate the ‘existence’ of a vendor or confirm if it is fictitious. Before calling it a day, a report needs to be drafted to conclude the assignment. In the meanwhile, the investigator could discover some evidence on another case and find a missing link in another suspected fraud.
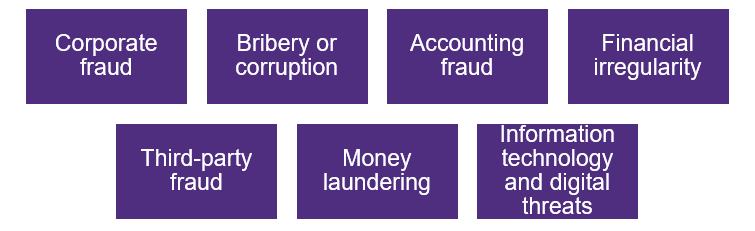
Illustrative spectrum of investigations
Fraudsters may have turned increasingly adept in hiding their trails, but there is always one weak link which initiates the first step in another climb for an investigator.
With contributions from Geetanjali Singh
